Know how Morfit Group Consulting can secure your web access with Zscaler Internet Access, a leader in the Gartner Magic Quadrant.

Zscaler Internet Access
ZIA has been the leader of Gartners’ Secure Web Gateway quadrant for 10 years in a row and is currently the ONLY vendor in the Gartner leaders quadrant.
As a SAAS security solution Zscaler accelerates enterprise cloud transformations, ensures and simplifies the integration of critical services like O365 and secures all your users everywhere.
Zscaler enables enterprises to transform to newer SASE topologies which over 50% of enterprises in Europe believe would enable IT to become a growth engine and contribute to the enterprise bottom line.

Zscaler Private Access
VPNs have been the mainstay of remote access solutions for decades now. However as highlighted by the increase in security breaches throughout COVID, increasing your remote or mobile workforce with VPNs also increases your threat surface. Zero Trust Network Access (ZTNA) is secure remote access solution replacing VPNs.
Zscaler Private Access (ZPA) is a ZTNA cloud service that provides seamless, zero trust access to private applications running on public cloud or within the datacentre. With ZPA applications are never exposed to the internet, making them completely invisible to unauthorised users. The service enables the applications to connect to users via inside-out connectivity versus extending the network to them. Users are never placed on the network. ZPA supports both managed and unmanaged devices and any private application (not just web apps) – providing a highly secure remote access solution not just for onsite applications and services, but also for cloud applications and services.
Know how Morfit Group Consulting can create a Zero Trust Network to protect your private applications with Zscaler Private Access.
Citrix Digital Workspace

Discover a better way to meet the needs of the modern workforce
The way we work is changing. Today’s remote workforce no longer views work as a place people go, but rather as something they do. Now more than ever, employees need a reliable way to work from any location—on any device, at any time. Which means it’s time for the traditional workplace to step aside for a much more modern workspace. By adopting a work-from-anywhere “digital workplace” model— one that’s not tied to any one geography, network or set of devices—amazing things can happen. It’s the kind of digital transformation that quickly leads to a superior user experience, increased employee engagement and greater productivity.
This is precisely what Citrix digital workspaces are designed to help businesses achieve.
Citrix Digital Workspace solutions empower companies to securely deliver the apps and data people need to be as productive as possible – no matter where they work or which device they use.
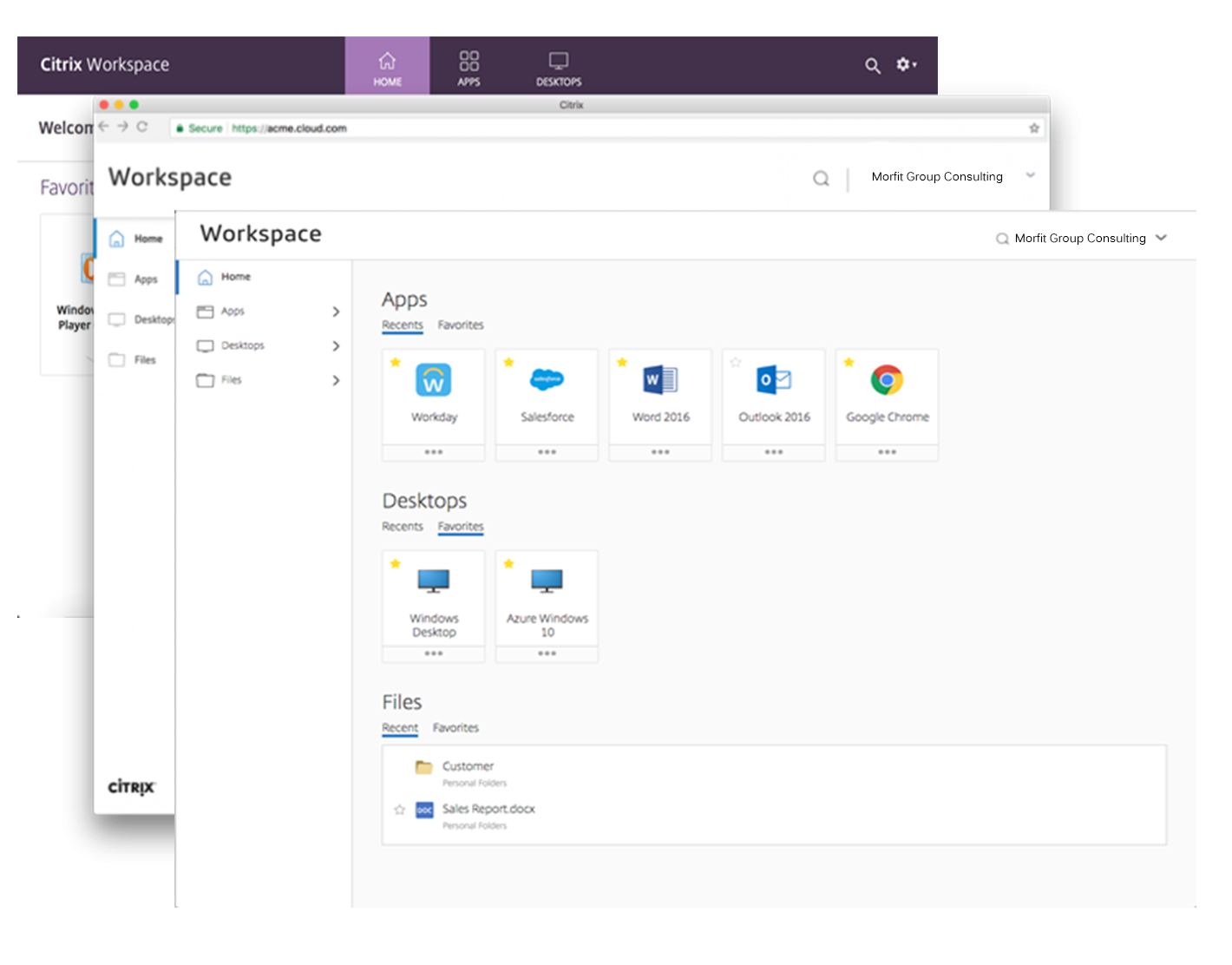
See how Citrix Digital Workspace solves your business and IT challenges.
Learn how Morfit Group Consulting can help your business power a smarter way to work with Citrix Workspace
Citrix Virtual Apps and Desktop
Citrix VDI and DaaS solutions empower companies to deploy secure, remote apps and desktop to users at scale – while providing a great experience and simplifying IT management.


Today’s employees spend more time than ever working remotely, causing companies to rethink how IT services should be delivered. To modernize infrastructure and maximize efficiency, many are turning to desktop as a service (DaaS) to enhance their physical desktop strategy, or they are updating on-premises virtual desktop infrastructure (VDI) deployments. Managed in the cloud, these deployments are high-performance virtual instances of desktops and apps that can be delivered from any datacenter or public cloud provider.
DaaS and VDI capabilities provide corporate data protection as well as an easily accessible hybrid work solution for employees. Because all data is stored securely in the cloud or datacenter, rather than on devices, end-users can work securely from anywhere, on any device, and over any network—all with a fully IT-provided experience. IT also gains the benefit of centralized management, so they can scale their environments quickly and easily. By separating endpoints and corporate data, resources stay protected even if the devices are compromised.
As a leading VDI and DaaS provider, Citrix provides the capabilities organizations need for deploying virtual apps and desktops to reduce downtime, increase security, and alleviate the many challenges associated with traditional desktop management.
See how Citrix VDI and DaaS solves your business and IT challenges.
Learn how Morfit Group Consulting can help your business create an outstanding experience with Citrix VDI and DaaS
Citrix Application Delivery Controller
Citrix application delivery controller solutions make it remarkably easy for organizations to gain operational consistency, holistic visibility, and comprehensive security across multi-cloud environments. This suite of technologies streamlines application delivery, providing actionable insights for faster troubleshooting, enabling easy-to-deploy web app and API protection—and much more. Providing an optimal experience for your application end users doesn’t have to be difficult.
Across industries—including banking, education, government, healthcare, and retail—organizations are modernizing apps by transitioning from monolithic to microservices-based architectures and by shifting workloads from on-premises environments to public and private clouds. As these apps fast become the lifeblood of organizational success, consistency is key. But frequently, transitioning to hybrid multi-cloud can create unwanted complexity.
Cultivating a competitive advantage means maintaining high-performing applications. And high-performing apps require high-performing infrastructure—the kind that eliminates the complications of multi-cloud application delivery management and help ensure a consistent security posture, all while empowering you to get to market faster.
Citrix Application Delivery Controller allow you to troubleshoot faster, provide a better user experience and strengthen your security posture across all applications and APIs.
See how Citrix Application Delivery solves your business and IT challenges.
Learn how Morfit Group Consulting can help your business gain all the insights you need with Citrix ADC
Citrix SD-WAN
Ensure all remote users are connected and secure
Citrix SD-WAN solutions allow organizations to provide secure, reliable access to business applications—no matter where they’re deployed or which devices and networks are used. This technology is becoming especially critical in the era of hybrid work environments, where employees frequently work away from branch offices. Lean More
See how Citrix SD-WAN solves your business and IT challenges.
Citrix SASE
Deliver fast, secure, and reliable access to all applications, for all users with a unified approach to SASE
Citrix Secure Access Service Edge (SASE) solutions bring together SD-WAN, zero trust access and comprehensive, cloud-delivered security into a single, centralized architecture. Together, these unified solutions allow organizations to provide secure remote access to applications and the internet, without putting strain on IT. And they’re built to meet the complex needs of distributed workforces. Lean More
Learn how Morfit Group Consulting can help you accelerate your cloud transition with Citrix

Silverfort was designed to protect areas that were previously thought un-protectable and is a proxy-less and agent-less solution enabling a quick and simple implementation.

Use Cases
Extending Multi-Factor authentication to systems that couldn’t be protected before (file shares, IT infrastructure, databases, command line (psExec, Powershell, OT systems and legacy onsite applications, etc).
Protecting service accounts used for machine-to-machine access.
Enforce risk-based authentication and zero-trust policies across all users and applications.
Enable organisations to migrate assets to the cloud securely.
“Radware knows DDoS attacks better than anyone”
The Forrester Wave: DDoS Mitigation Solutions, Q1 2021
Forrester ranked Radware as a leader for DDoS protection and the evaluation gave Radware the highest score in the current offering category.

Radware Cloud DDoS Protection Service
What Does Cloud DDoS Protection Service Do?
Distributed denial-of-service (DDoS) attacks are becoming more frequent, more powerful and more sophisticated. With the growing availability of attack tools and global botnets, the pool of possible attacks is larger than ever. Relying on humans to prevent and block attacks is simply not enough, and organizations dependent on manual-based DDoS protection and mitigation services are not fully protected from today’s threats.

Three Cloud DDoS Protection Services
1. Hybrid Cloud DDoS Protection Service
Radware’s Hybrid Cloud DDoS Protection service integrates with Radware’s on-premise DDoS protection device. Recommended for organizations that can deploy an on-premise device in its data center, Hybrid Cloud DDoS Protection Service delivers: Minimal induced latency in peacetime, Shortest time to protection, No protection gap, and Single point of contact and extensive managed services.
2. Always-On Cloud DDoS Protection Services
Radware’s Always-On Cloud DDoS Protection Service provides always-on protection where traffic is always routed through Radware’s cloud security POPs (Points of Presence) with no on-premise device required for detection and mitigation.
Recommended for organizations that have applications hosted in the cloud or those that are not able to deploy an on-premise attack mitigation device in their data center, Always-On Cloud DDoS Protection Service delivers: Shortest time to protection, Minimal customer involvement, and Rapid onboarding process.
3. On-Demand Cloud DDoS Protection Service
Radware’s On-Demand Cloud DDoS Protection Service protects against Internet pipe saturation and is activated when the attack threatens to saturate the organization’s Internet pipe.
Recommended for organizations that are looking for the lowest cost solution and are less sensitive to real-time detection of application-level and SSL-based DDoS attacks, On-Demand Cloud DDoS Protection Service delivers: On-demand attack mitigaion, Traffic diverted into cloud only upon volumetric DDoS attacks, and Diversion based on link utilization thresholds, flow statistics, or manually.
Learn how Morfit Group Consulting can help your business protect itself from DDoS attacks using Radware Cloud DDoS Protection Service. A leader in DDoS protection.
Radware Web Application Firewall (WAF) and Bot Manager

What Does AppWall Do?
AppWall – Radware’s Web Application Firewall (WAF), ensures fast, reliable and secure delivery of mission-critical Web applications and APIs for corporate networks and in the cloud. AppWall is an NSS recommended, ICSA Labs certified and PCI compliant WAF that combines positive and negative security models to provide complete protection against web application attacks, access violations, attacks disguised behind CDNs, API manipulations, advanced HTTP attacks (slowloris, dynamic floods), brute force attacks on login pages and more.
At the core of Radware’s web application and API protection Solution suite, AppWall is a web application firewall (WAF) that provides patent-protected technology to create and optimize security policies in real-time for widest security coverage with the lowest false positives and minimal operational effort. Radware’s Web application security technology features a variety of deployment modes – as a stand-alone or integrated on an ADC, on-premise and in the cloud, inline or out-of-band, and even a Kubernetes edition.
What Does Radware Bot Manager?
Radware Bot Manager provides comprehensive protection of web applications, mobile apps and APIs from automated threats like bots. Bot Manager provides precise bot management across all channels by combining behavioral modeling for granular intent analysis, collective bot intelligence and fingerprinting of browsers, devices and machines. It protects against all forms of account takeover (credential stuffing, brute force etc.), denial of inventory, DDoS, ad and payment fraud and web scraping to help organizations safeguard and grow their online operations.

Learn how Morfit Group Consulting can help your business differeniate bad bots from good bots with Radware
Radware Cloud Workload Protection
Keep Your Cloud Infrastructure Safe and Secure
Migrating workloads to the public cloud creates new threat surfaces which can be exploited by attackersᅠand lead to theft of your customers’ data.
Radware provides comprehensive protection for applications hosted on AWS and Azure with multi-layer defenses which secure the cloud environment against identity and access abuse, protect against malicious user behavior, and secure the overall security posture of the public cloud environment.

Multi-Layered Protection for Public Cloud Infrastructure
Radware’s Cloud Native Protector provides multi-layered protection for application infrastructure and workloads hosted in public cloud environments, to prevent accidental exposure, misconfigurations, and malicious activity in the cloud environment.
Cross-Cloud, Actionable Visibility and Control
Radware provides centralized workload security management with single-pane-of-glass controls and multi-cloud support for AWS and Azure workloads. Automated discovery of cloud asset inventory and a unified view of assets across multiple accounts, regions, and environments within a single dashboard is also provided.
Learn how Morfit Group Consulting can help keep your cloud infrastructure safe and secure with Radware CWP
In the battle against ever-evolving cyber threats, we need to act faster and smarter than what’s possible with human-powered technology. SentinelOne is autonomous cybersecurity built for what’s next. Endpoint security software that defends every endpoint against every type of attack, at every stage in the threat lifecycle.
One Platform.Three Reasons to Believe.
Best-in-Class Technology
Singularity™ sets the standard for modern security platforms with unparalleled visibility of what’s on your network and enterprise-grade automation & control. Rich AI models enable every endpoint and cloud workload to autonomously prevent, detect, and recover from threats in real time.
Performance Advantage
SentinelOne is committed to the success of our customers, from small IT shops to leading Fortune 10 enterprises; we know that the love is mutual from our 98% satisfaction rate. Teams everywhere trust our MDR & DFIR experts to block and eradicate some of the world’s largest breaches.
Industry Recognition & Results
SentinelOne is a proud Leader in the enterprise security market. We have been recognized for our execution and innovation by authorities such as Gartner, and we consistently lead the pack in testing & evaluations conducted by firms such as MITRE Engenuity and SE Labs.

SentinelOne Leads 2020 MITRE ATT&CK Evaluation as Only Vendor to Deliver 100% Visibility
SentinelOne is Redefining Cybersecurity by Pushing the Boundaries of Autonomous Technology

Actionable XDR
See what’s possible beyond just identifying malicious behaviors. Block and remediate advanced attacks at machine speed with cross-platform, enterprise-scale data analytics.

Distributed AI
Equip every endpoint and workload—no matter their location or connectivity—to respond intelligently against cyber threats with powerful static & behavioral AI.

Storyline™
Empower analysts with the context they need, faster, by automatically connecting & correlating benign and malicious events collected over weeks to years in one illustrative view.

Learn how Morfit Group Consulting can help your business protect its endpoints with SentinelOne using its advance AI endpoint security platform

Assure security readiness across your complete attack surface With the Pentera Automated Security Validation™ Platform
What is Automated Security Validation
Security professionals are continually searching for their real cybersecurity gaps amongst the overload of vulnerability data. We have come to accept assumptions as the norm given the inaccurate, stale, and context-lacking data in our vulnerability management systems.
With IT infrastructure and cyber threats evolving faster, it is critically important that real vulnerabilities are treated before they are exploited. While penetration testing services may pinpoint such threats accurately, these services cannot scale in scope or be applied in a continuous manner.
True knowledge of our exposure enables us to focus our resources on fixing the real security gaps. Automated Security Validation (SecVal) is how we flip on the light to focus on our real security gaps and guide cost-effective remediation. With it, cyber professionals can surgically remediate with fresh data that is based on threats’ real impact on their business.
Shift from operating under assumptions to embracing clarity.
Learn how Morfit Group Consulting can help your business increase its efficiency and effectiveness with Pentera

Your Cloud Expectations, Exceeded.
Successfully moving into the cloud depends on more than just the right platform, it requires the right cloud partner
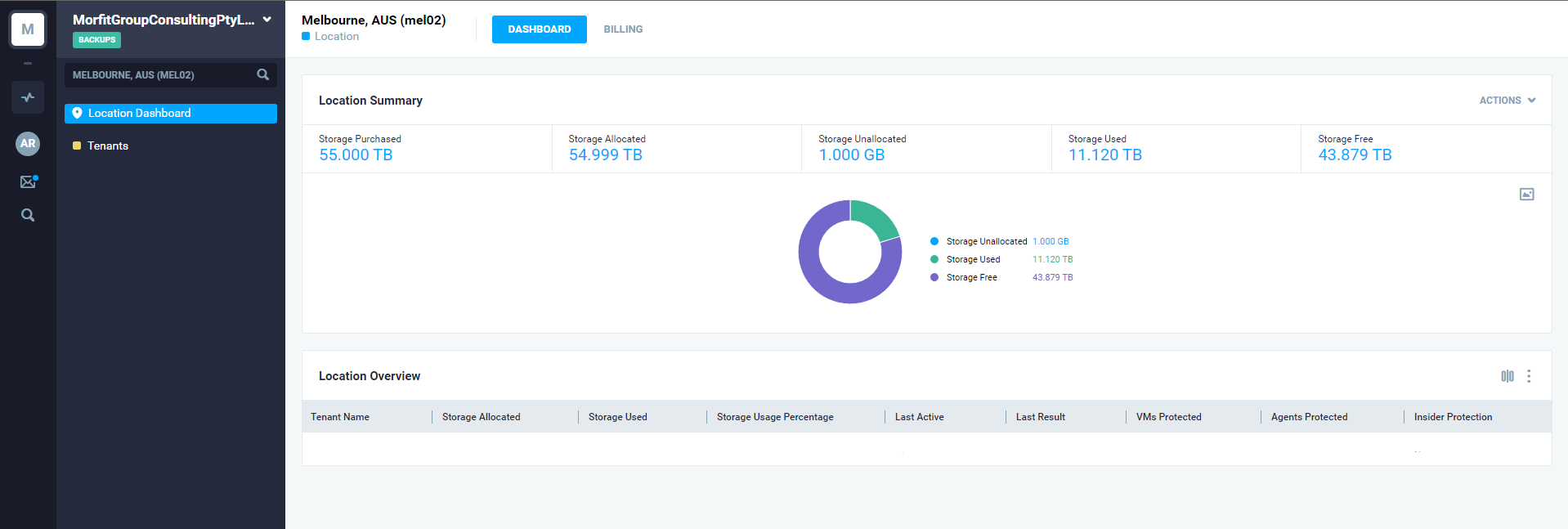
Successful Clouds Starts with the Right Foundation
The iland Cloud Platform provides the foundation for a complete cloud transformation, while giving you the proven technology you need for a true competitive advantage.
GET IN TOUCH TODAY
Contact us directly via the button below!
Address
Level 24
570 Bourke St
Melbourne VIC 3000
Australia
Copyright © 2024 Morfit Group Consulting







